
Las nuevas características del Sistema Operativo (Big-IP V13) de la empresa F5 Networks.
BIG-IP LTM NUEVAS CARACTERISTICAS:
-
Health Monitor Statistics:
Esta característica permite tener estadísticas de los monitores y las instancias que se tienen sobre los servicios, de la siguiente forma:
Monitoreo del monitor:
My_HTTP_Monitor
o Probe_count 717
o Probe_success 614
oProbe_failure 89
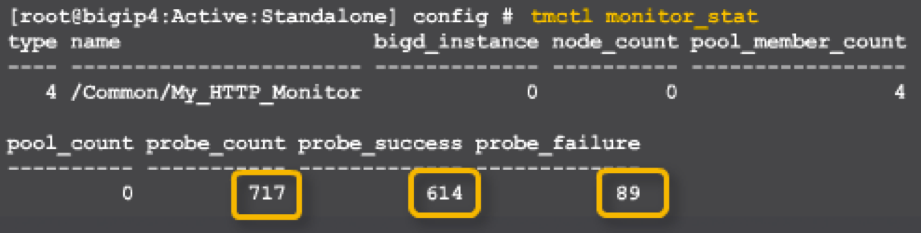
My_HTTP_Monitor instance 172.16.20.1:80
o Probe_count 181
o Probe_success 79
o Probe_failure 89
-
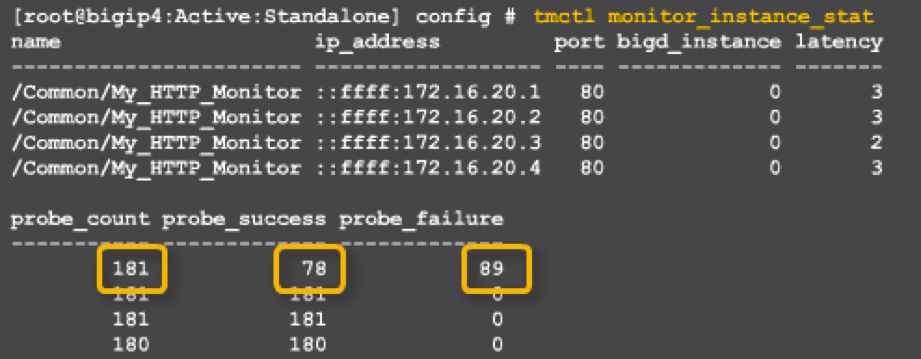
TCP Profiles:
Se crearon unos nuevos y mejorados perfiles que ayudan con la optimización de las aplicaciones, sin embargo, los anteriores no se eliminan, dado que muchos pudieron haber creado perfiles basados en estos.
Los perfiles f5-tcp-wan, f5-tcp-lan, f5-tcp-mobile son versiones actuales de tcp-wan-optimized, tcp-lan-optimized y tcp-optimizado donde se incorporaron las características más recientes. El perfil f5-tcp-progressive el cual es un perfil de propósito general.
Según indica el fabricante estos 4 perfiles nuevos serán actualizados con las mejores prácticas a medida que evolucionen.
Leer mas sobre el nuevo esquema de profiles https://devcentral.f5.com/articles/f5-unveils-new-built-in-tcp-profiles-25175
-
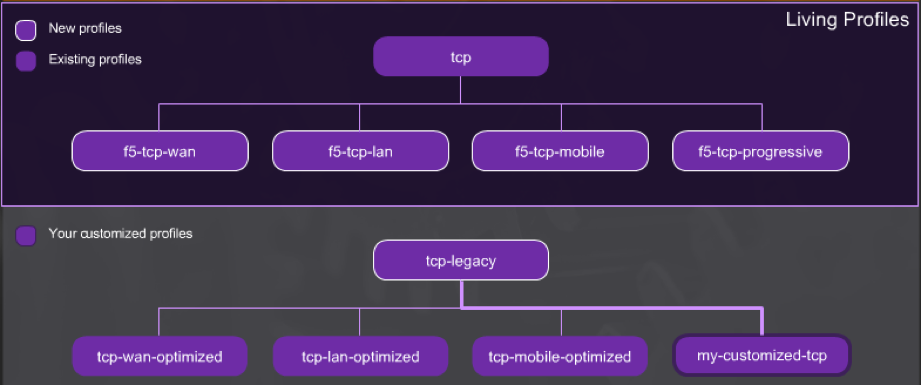
HA Troubleshooting Enhancements:
Ayudando a un diagnóstico más rápido y sectorizado al momento de configurar y/o soportar “HA”, en la nueva versión se han incorporado nuevos mensajes y comandos.
-
Otras características y Mejoras
-
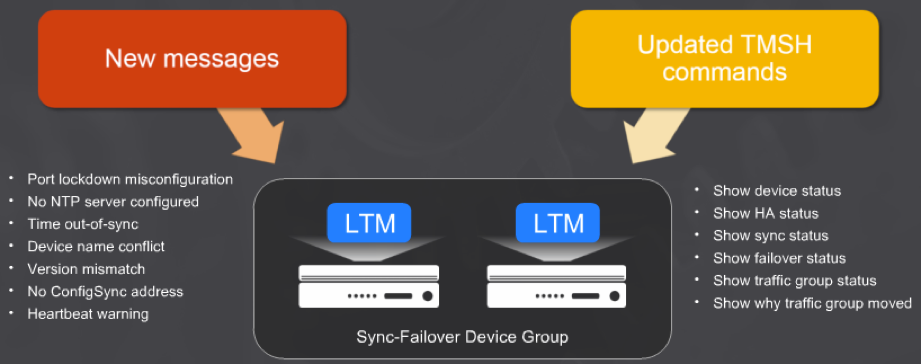
Cipher Rules and Cipher Groups :
Esta versión introduce grupos y reglas de cipher que permiten visualizar, organizar y aplicar conjuntos de cifrado; los grupos son manejados con los siguientes operadores boleanos:
UNION = permite todo.
INTERSECT = Permite únicamente lo que se encuentra en A y B.
DIFFERENCE = Se excluye lo que se indique.
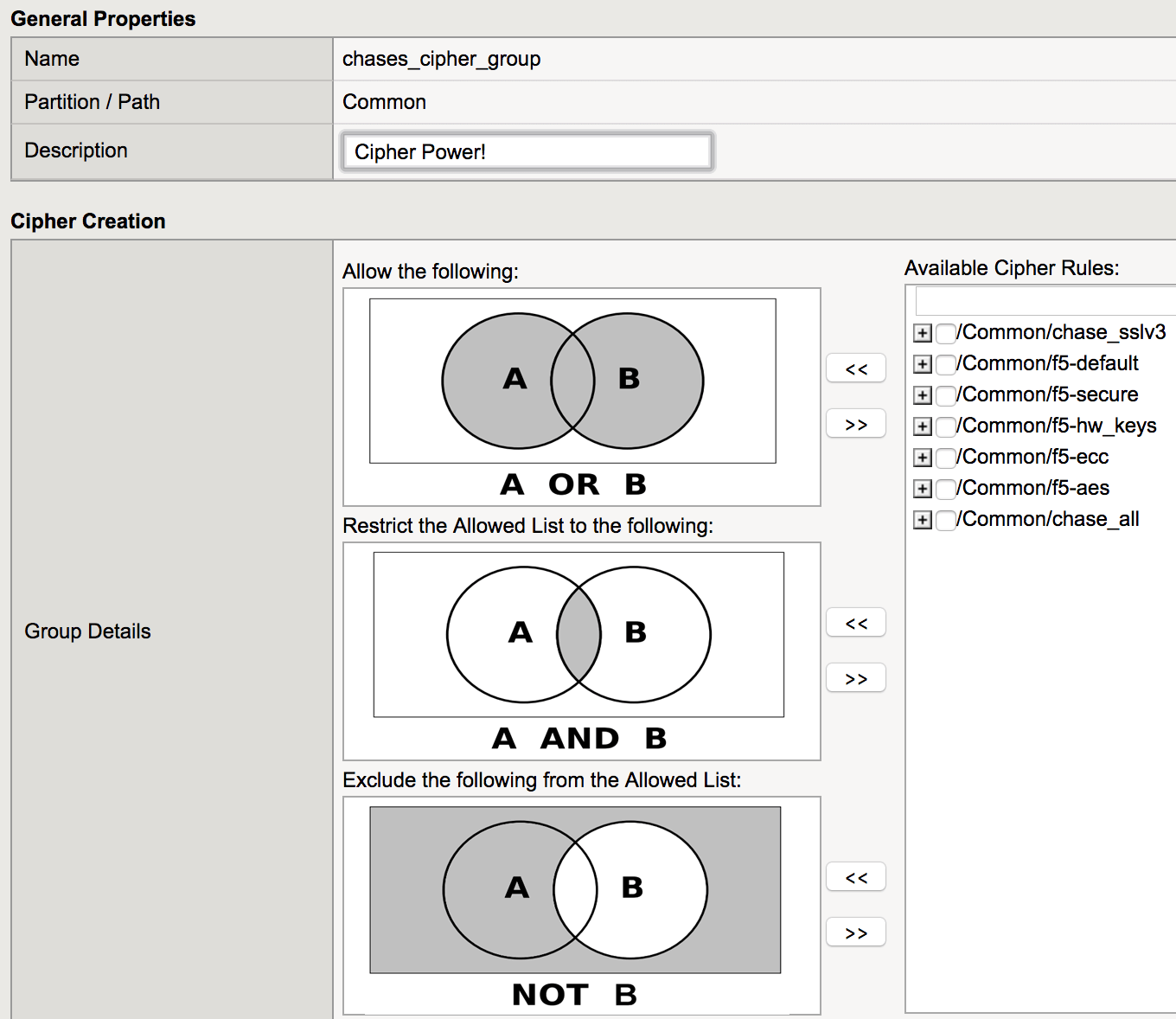
Leer mas sobre grupos y relas de Cipher https://devcentral.f5.com/articles/cipher-rules-and-groups-in-big-ip-v13-25200
-
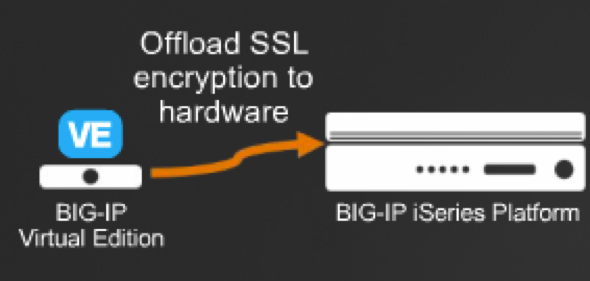
Elliptical curve crypto (ECC) support for F5 external crypto offload:
Permite delegar la carga de las operaciones criptográficas de una versión virtual a una versión física.
-
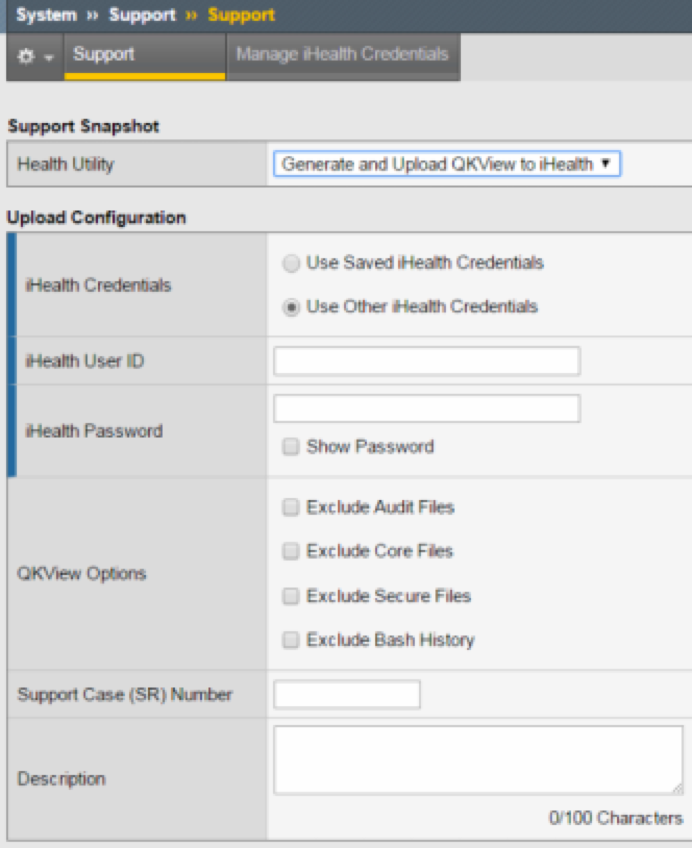
Subir el archivo de diagnóstico QKVIEW directamente al iHealth.











work? I've very little understanding of coding but I was hoping to start my own blog soon. Anyways,
should you have any ideas or techniques for new blog owners please
share. I know this is off subject nevertheless I simply needed to ask.
Appreciate it!
мешки для мусора 160 л [url=https://meshki-dlya-musora-160-litrov.ru/]мешки мусорные 160 л цена[/url].
and electromagnetic railguns or coilguns. A qualified HVAC technician knows how to handle capacitors safely and effectively.
A professional HVAC contractor will take a comprehensive look at your system and
offer the right guidance. Additionally, you
could void your warranty by working on the air conditioner without the right qualifications.
Many people are working in other projects to develop XML-based standards for
information such as graphics (SVG), molecular structures, buildings
and CA drawings, etc. We will use a general XML-to-XML conversion engine (possibly
Ricoh's PIA), that is available for any component to use.
Capacitors are connected in parallel with the DC power circuits of most electronic
devices to smooth current fluctuations for signal or control circuits.
They can also be used in charge pump circuits as the energy storage element in the
generation of higher voltages than the input voltage.
Because capacitors pass AC but block DC signals (when charged up
to the applied DC voltage), they are often used to separate the AC and DC components of a signal.
Do you have any tips on how to get listed in Yahoo News?
I've been trying for a while but I never seem to get there!
Many thanks
I am impressed! Very useful information specially the last part :
) I care for such information much. I was seeking this particular info for
a very long time. Thank you and good luck.
Is going to be again frequently to investigate cross-check new
posts
get benefit from it I am sure.
Market Torrez Darknet
onion darknet Torrez
The darknet market is a hidden part of the internet where illegal activities thrive. While it can be intriguing to explore this clandestine world, it is essential to understand the risks and consequences associated with such actions. The allure of anonymity and the ability to engage in illicit activities may be tempting, but individuals must consider the potential legal, financial, and personal risks before venturing into the darknet market.
people, due to it's good articles or reviews
to generate a great article… but what can I say… I hesitate a lot and
never seem to get anything done.
I must spend some time learning more or understanding more.
Thank you for fantastic info I used to be in search of this information for my mission.
web site came up, it looks good. I have bookmarked it in my google bookmarks.
Hello there, just changed into alert to your blog via Google, and found that it is truly informative.
I'm going to be careful for brussels. I will appreciate in the event you continue this in future.
A lot of folks will be benefited from your writing.
Cheers!
not happened earlier! I bookmarked it.